Bank Executives Implicated in Cyber Fraud: Global Law Enforcement Cracks Down with Arrests
Three chiefs from Kotak Mahindra Bank were caught for their association in supporting cybercriminals in swindling people across India of crores. They achieved this by clandestinely opening 2,000 ledgers. As a result of their activities, they were captured.
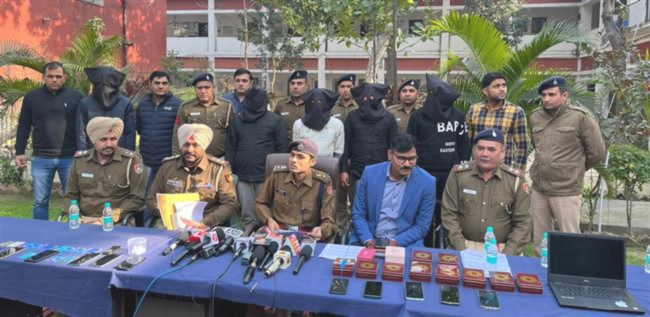
On Tuesday, police authorities unveiled that three chiefs from a confidential bank in Guru gram had been secured. Their capture related to charges of intrigue with a cybercriminal pack, working with the cheating of thousands of individuals from one side of the country to the other, adding up to crores of rupees.
As per cops, two representative directors and an associate chief from Kotak Mahindra Bank’s MG Street branch are ensnared in a plan where they purportedly opened north of 2,000 financial balances throughout the course of recent months in line with cybercriminals. These hoodlums would channel cash taken from casualties cross-country into these records, which the leaders worked with. In this manner, the badly got reserves were removed utilizing charge cards given by the bank authorities. The officials further referenced that the leaders got at least, ₹15000 in real money for each record they helped with opening.
A representative for Kotak Mahindra Bank gave an assertion affirming that the three workers are being scrutinized by the cybercrime police in Caesar. The examination originates from a grievance documented by an individual blaming them for cheating him. The bank states its commitment to security and consistence, stressing participation with experts in the continuous examination.
Colleague Chief of Police (Cybercrime) Priyanshu Dewan recognized the three confined leaders as Mahesh Kumar (27) and Vishwakarma Maurya (28), both filling in as delegate supervisors, alongside Mohit Rath (25), an associate administrator. Furthermore, examiners uncovered the misgiving of another suspect, Mohammad Hay at (22), subsidiary with the digital fraudsters’ pack situated in Nun. ACP Dewan framed Hay at’s job, which included providing the bank chiefs with fake SIM cards for opening ledgers, dispensing their bonus in real money, and recovering the check cards.

“Through our cross-examination of the three financiers, we’ve found they’ve been engaged with opening at least 2,000 dubious fashioned accounts throughout recent months. Be that as it may, we’ve officially mentioned a far-reaching report from the bank to discover the all out number of records the suspects opened. Alongside subtleties on the number of records that had their data or contact numbers modified utilizing the suspects’ login qualifications. These specialized particulars are urgent in understanding the degree of the misrepresentation they executed by conniving with the pack,” expressed ACP Dewan.
The examination unfurled following a complaint stopped by a resigned Line Security Power part on February 17, claiming a deceitful exchange adding up to ₹10,000. As per the complainant, the trickery started with a call got on November 18 the earlier year, purportedly from a recognizable number. The guest, acting like a companion, mentioned a UPI move of ₹25,000.
After quickly moving ₹10,000 to the gave UPI address, the complainant became watchful and chosen to check the solicitation. Reaching his companion straightforwardly, he found the call had not started from them, nor had they mentioned any assets. Acknowledging he had succumbed to a trick, the complainant recorded an authority report. The objection was held up at the cybercrime police headquarters and enlisted under areas 419 (cheating by personation), 420 (cheating), and 120B (criminal connivance) of the Indian Corrective Code.
During the examination, police distinguished the contribution of four suspects for the situation. Rath was secured from Bilaspur on February 21, trailed by Kumar’s capture in ALADI the resulting day. Furthermore, Maurya was kept in Caesar, and Khayat in Mew at, on Monday, under the management of Examiner San dip Atlanta, the station house official of cybercrime (Caesar). By and by, each of the four are in police guardianship for additional cross-examination.
Siddharth Jain, the appointee magistrate of police (cybercrime), underscored that the cross-examination cycle would reveal insight into whether extra bank authorities were complicit in the wrongdoing. “Kumar has a past work history with a non-banking monetary company, Maurya with a little money bank in Area 15 Section 1, and Rath with one more confidential bank in Area 15. We plan to connect with their previous businesses to assemble data pretty much every one of the records they took care of during their residency,” Jain expressed. He highlighted the uniqueness of this case, featuring it as the primary example where direct contribution of bank chiefs has been uncovered as a team with a cybercrime group working for an enormous scope. From one side of the country to the other.
“We’ve seized their cell phones. In practically no time, we’ll advance the case specifics to the Indian Cybercrime Coordination Center under the Association Service of Home Issues. We’ll find out the exact count of casualties and the degree of the pack’s money related gains,” he asserted. Jain noticed that roughly 40–50 individuals from the group, alongside its forerunner in Nun, stay at large. Endeavours are effectively in progress to secure them at the earliest open door.
“We’ve seized their cell phones. In no time, we’ll advance the case specifics to the Indian Cybercrime Coordination Center under the Association Service of Home Issues to determine the exact count of casualties and the degree of the group’s financial additions,” he confirmed. Jain noticed that around 40–50 individuals from the pack, alongside its forerunner in Nun, stay at large. Endeavours are effectively in progress to catch them at the earliest open door.
In the meantime, ACP Dewan revealed that Khayat had recently filled in as a boss at an online business company’s distribution centre in Bilaspur, where he encountered Kumar something like quite a while back. “After leaving from his work, Khayat became related with the cybercrime organization. In the meantime, Kumar started his residency at Kotak Mahindra Bank. Around seven to eight months prior, Khayat started contact with him, and they have been teaming up from that point forward,” Dewan made sense of.
The triplet regularly visited Bilaspur and Farrukhnagar, explicitly focusing on day-to-day wage labourers and workers from lower-pay bunches related with internet business organizations to request account openings.
Khayat’s job included venturing out from Mew at to Bilaspur, giving fake SIM cards, and dispensing cash commissions to Kumar and Rath. Consequently, he would recover charge cards from them once the financial balances were initiated. The agents noticed that Khayat likewise accompanied Kumar to Mew at, acquainting him with the head of his group.
According to the police, each phony SIM card was utilized to enact three to four records. On the off chance that a candidate’s certifiable portable number was at that point in the bank’s records, the administrators would substitute it with the one given by the posse chief through Khayat. Examiners clarified that the suspects used fake SIM cards in their gadgets to validate the linkage of the portable number with the records. Hence, they eliminated the SIM cards and packaged them into units to give up to Khayat. For each false record unit got from the investors, Khayat got a commission of ₹3,000.
Subscribe To Our Channel :- YouTube, Daily News Country, Face book